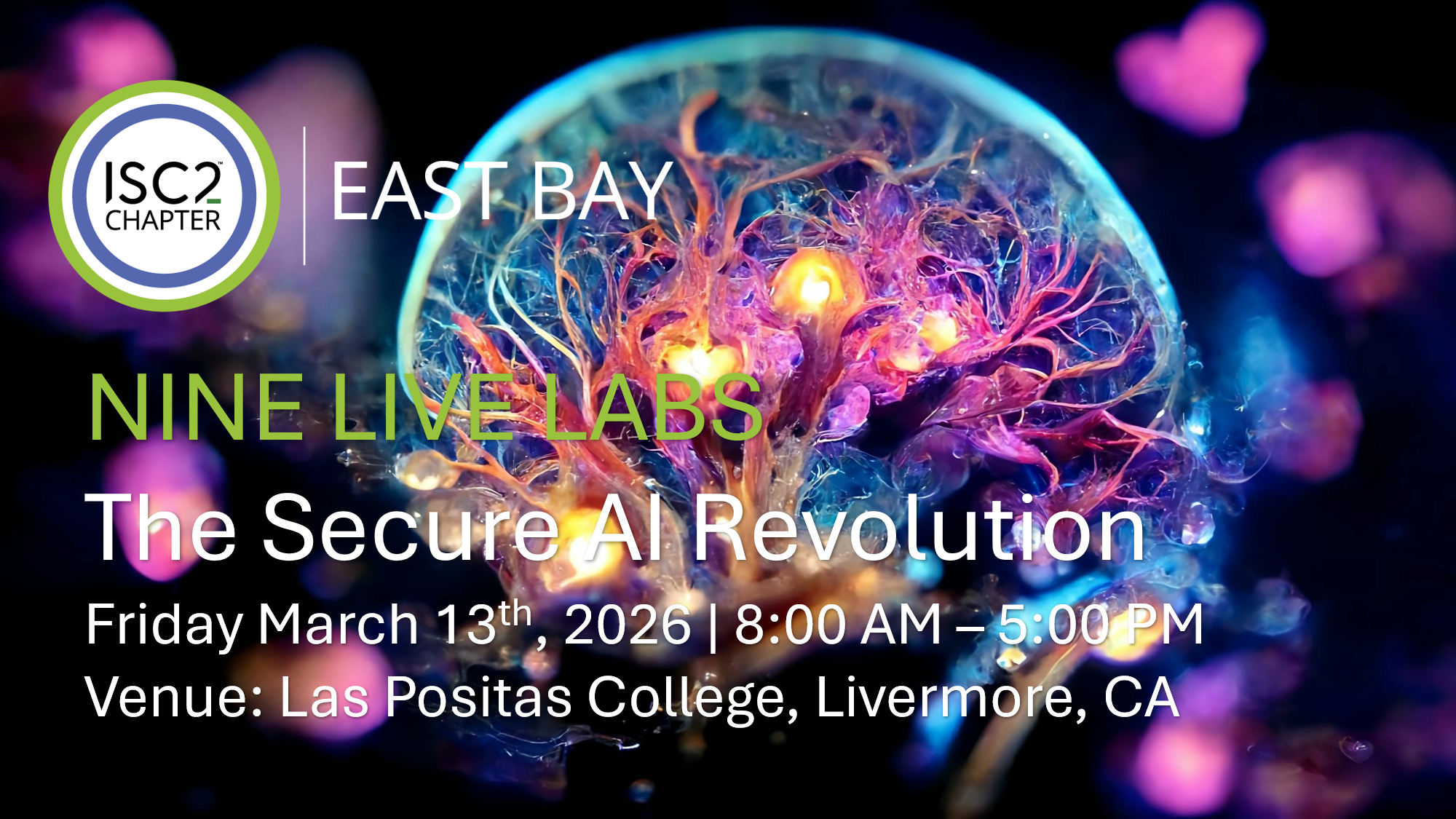
Venue: Las Positas College, 3000 Campus Loop, Bld 1000, Livermore, CA Date and Time: March 13, 2026 | 8:00 AM – 5:00 PM The Secure AI
Author: Robin Basham

ISC2 East Bay Chapter is a PROUD PARTNER of the Silicon Valley Cybersecurity Summit, and we invite our actively employed IT Security Team and Cybersecurity

Registration required: April 10, 2025 – 7:00pm – 9:00pm Pacific Time | 2 CPEs Bylaws Update We are presenting the revised bylaws of the ISC2
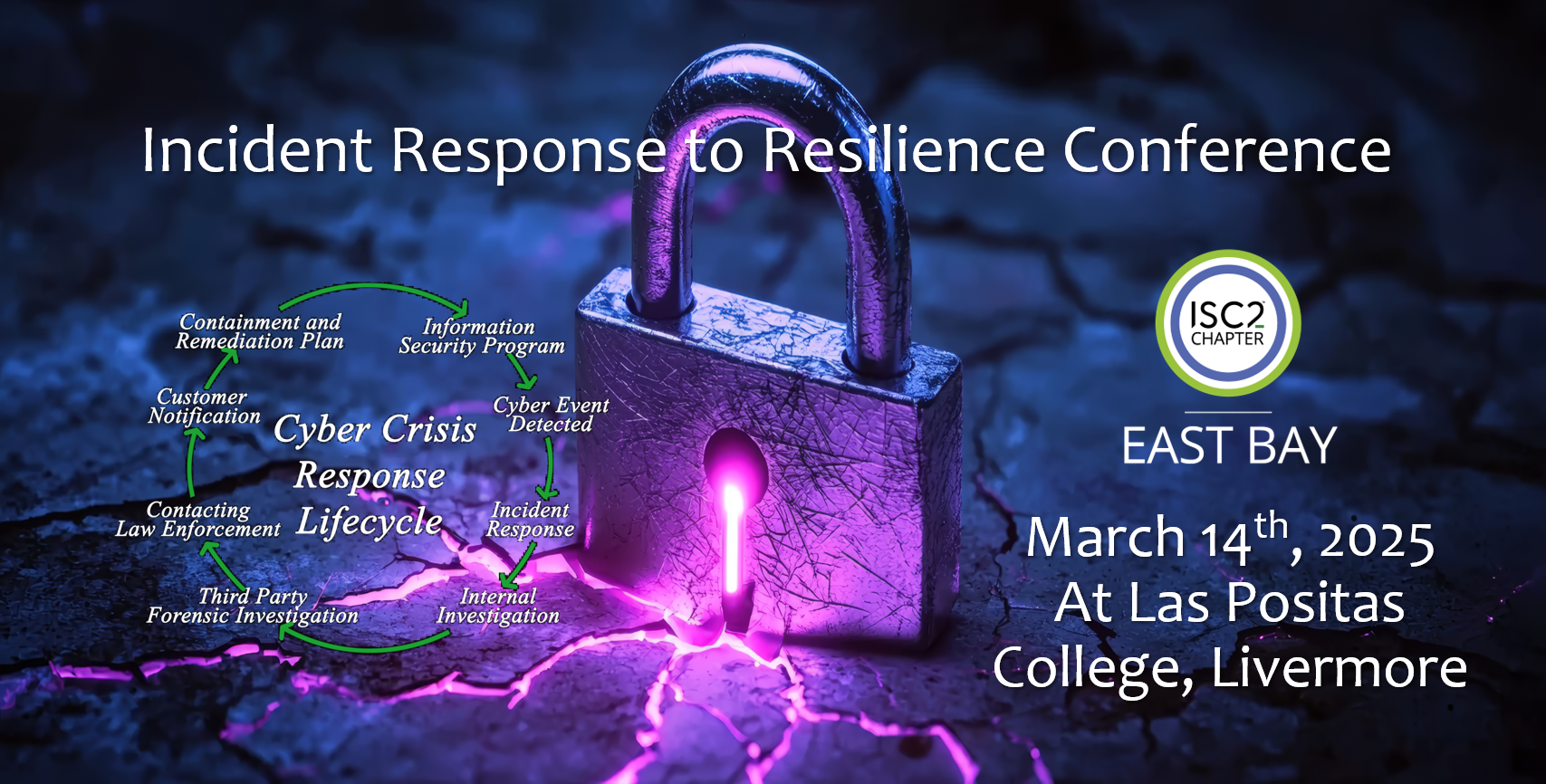
Registration has ended. Members can access playback to selected sessions below. Held on the Livermore campus of Las Positas College, our speaker events combine large

ISC2 East Bay member and past sponsor Lauren Arce has again extended limited invitations to the women of ISC2 East Bay. This is a first

Learn how to protect yourself & your business from becoming a victim of cybercrime. Save the date and join us for the 9th Annual Official

*Sales have ended for this event. Email robin.basham@isc2-eastbay-chapter.org for questions or concerns about registration. Our one-day event will be held on the Livermore campus of

March 8th, 2024 | 8:00 AM to 5:00 PM | Dublin, California Speakers from the most prestigious standards organizations and companies in Healthcare and Healthtech

We are pleased to offer you the “2024 Insider Threat Report” based on a survey of 450 cybersecurity professionals. As insider threats continue to pose

November 10, 2023, | 8:00 AM Breakfast and registration, to 5:00 PM | Dublin, California Registration is closed as we are at capacity. Speakers from
Attention: We are at capacity. If you recieved an email stating you have a badge, you can come. If you have not been notified that

Gathering the Gals for an Afternoon Tea, our Vice President has coordinated an invitation for Women-in-Cyber business networking. Sponsored by ColorTokens and Optiv, our female