March 8th, 2024 | 8:00 AM to 5:00 PM | Dublin, California
Speakers from the most prestigious standards organizations and companies in Healthcare and Healthtech gather to share emerging and important considerations, strategies, tools, platforms, and standards necessary for Cyber Professionals managing Cybersecurity in Healthtech and Health Management. We are honored to be invited to hold this exclusive event at the new ZEISS Innovation Center.

The conference is at capacity. Walk-ins are strictly prohibited. Conference Speakers and Conference Committees are not required to register. You are not fully registered if you have not received your ISC2 East Bay Conference Feedback Form. In that event, you may contact robin.basham@isc2-eastbay-chapter.org, President & Conference Chair.
Attendees receive up to 8 CPEs for attending and providing their participation feedback. Conference Committee volunteers earn up to 13 CPEs.

Conference Sessions & Schedule
Greetings Message from our Venue-Sponsor, ZEISS
8:00 AM to 8:50 AM | Registration, Breakfast, and a walking tour of the most amazing venue experience our chapter has ever known. Learn more of what we have in store on the beautiful Dublin Campus of ZEISS. Breakfast includes muffins and pastries with fresh sliced fruit, juice, coffee & tea.

Session One – 9:05 to 9:55 AM | Cybersecurity in Medical Devices at ZEISS | co-presented by Sunil Kulkarni, David Best, and Peter Boaz
Dave Best, Jr – US Head of Product Cybersecurity and Privacy | CISSP, Medical Technology Business Group

US Head of Product Cybersecurity and Privacy
ZEISS Medical Technology
About Dave Best: Mr. David Best, Jr is the Head of Product Cybersecurity and Privacy at Carl Zeiss Meditec AG. In this role, he oversees all activities related to product cybersecurity and data privacy for Zeiss Meditec. Mr. Best is responsible for the cybersecurity of Zeiss Meditec pre-market and post-market products, ensuring adherence to advanced security standards and regulatory compliance. Previously, Mr. Best served as a Senior Director for FTI Consulting’s Cybersecurity practice, focusing on regulatory compliance, cybersecurity risk assessments, vulnerability management, penetration testing, and incident response. Mr. Best also served as an advisor/consultant for corporations, helping them strengthen and secure their software development lifecycle. Mr. Best holds a B.S. in Electrical Engineering from Temple University and a M.S. in Software Engineering from Monmouth University. Mr. Best also holds an active CISSP certification.
Peter Boaz, Product Security Officer, ZEISS Medical Technology

Product Security Officer
ZEISS Medical Technology
About Peter Boaz: Peter is the Product Security Officer for Medical Devices at Carl Zeiss Meditec AG. In this role, he oversees the security and data protection of medical devices throughout their lifecycle, ensuring adherence to advanced security standards and regulatory compliance. Previously, Peter served as a Solutions Architect for Cloud Security at Optimizely, where he focused on privacy-compliant solutions. He also worked as a Data Protection and Privacy Consultant at HewardMills, advising corporations on data governance and compliance. Peter holds a J.D. from the University of California College of the Law, San Francisco, and a B.A. from George Washington University.
Sunil Kulkarni, Head of Cybersecurity R&D

ZEISS Ophthalmology
About Sunil Kulkarni: Sunil leads R&D of cybersecurity features in medical device products at ZEISS, Dublin, CA. This domain addresses special customer requirements such as those in the DHA RMF. Sunil is also responsible for post-market monitoring activities to ensure continued cybersecurity updates for customers. Before joining ZEISS, he was a senior R&D software manager at Philips.
About ZEISS: ZEISS is an internationally leading technology enterprise operating in the optics and optoelectronics industries. As a company wholly owned by a foundation, ZEISS is rooted in and committed to responsibility in all its activities.
“Our aim is contributing to progress in medical technology and helping healthcare professionals all over the world to improve their patients’ quality of life. With a special focus on ophthalmology, ophthalmic surgery and visualization systems in the field of microsurgery, the company supports healthcare professionals in setting new standards of care with proven medical technology and broad application competence based on cutting-edge innovations. ZEISS also offers visualization solutions for dental treatment and gynecology. The company’s medical technology portfolio is completed by future-oriented technologies such as intraoperative radiotherapy.”
Session Two – 10:00 to 10:30 AM | Generative AI in Data Security, Karthik Krishnan, CEO & Founder

Karthik is a co-founder and the CEO at Concentric. Before Concentric, he was VP of Security Products at Aruba/HPE, where he managed their security portfolio, which included the Niara acquisition and their network access control product lines. Before that, he was part of the founding team and VP of Products at Niara, a security analytics company focused on user and entity behavior analytics. Niara was acquired by Aruba/HPE last year. Niara was a leading user and entity behavior analytics (UEBA) company with several Fortune 50 companies as customers when it was acquired. He has over 15 years of extensive security and networking experience in leadership positions at several companies, including Juniper Networks, PGP, and Symantec. He has a Bachelor’s in engineering from the Indian Institute of Technology, Madras, India, and an MBA with distinction from the Kellogg School of Management, where he was an F.C. Austin Scholar.
Concentric AI With Concentric AI, organizations can finally address their unmet data security needs by discovering and protecting business-critical content. Concentric AI protects intellectual property, financial data, PII/PCI content, customer data, business confidential content, and more across on-premises and cloud-based data stores, as well as messaging and communication applications. The Concentric AI Semantic Intelligence™ Data
Session Three – 10:30 to 11:15 | Third-Party Vendor Risk Management | The Department of Public Health, City and County of San Francisco | Marc Upchurch, MBA, CISO

Marc Upchurch, MBA
Chief Information Security Officer at City and County of San Francisco – Department of Public Health
Topic: Top 10 DPH Concerns and Priorities Regarding Vendor/Third-Party Risk Assessment and Risk Management
In the context of third-party risk assessment and risk management for cybersecurity, the following are the top 10 concerns and priorities:
- Lack of Speed: Addressing the need for prompt assessments and responses to evolving threats and vulnerabilities associated with third-party engagement.
- Lack of Visibility: Ensuring complete visibility into third-party practices and potential vulnerabilities that might affect your organization.
- Lack of Context: Understanding the specific context of third-party risks, including industry-specific threats and regulatory requirements.
- Lack of Trackability: Implementing effective mechanisms to track and monitor third-party activities and compliance over time.
- Lack of Engagement: Encouraging active engagement and collaboration between your organization and third-party vendors to strengthen security posture.
- Continuous Preventive Procedure: Designing and executing ongoing preventive strategies rather than merely reactive measures in managing third-party risk.
- Risk Identification and Analysis: Conducting comprehensive risk identification and analysis as part of the cybersecurity risk assessment process.
- Documenting Sensitive Information Access: Clearly documenting the types of sensitive information accessible to third-party vendors and ensuring they adhere to appropriate security measures.
- Monitoring and Remediation: Continually assessing, monitoring, and remediating vendor information security, operational risks, and data privacy risks.
- Proactive Risk Management: Employing tools and strategies for proactive remediation of cyber risks in the supply chain, including continuous monitoring of third-party cybersecurity practices.
About our Speaker: “I am Marc Upchurch, the Chief Information Security Officer (CISO) at the Department of Public Health (DPH) of the City and County of San Francisco, the lead agency in the San Francisco Continuum of Care. I have over 20 years of experience in delivering strategic IT results for various sectors, including healthcare, finance, manufacturing, telecommunications, and retail. I hold ITIL and Oracle certifications, as well as an MBA in Management Information Systems.
As the CISO, I manage the cybersecurity strategy and operations for all on-premise, hosted, and cloud-based departmental systems, ensuring compliance with governmental security, privacy, and regulatory standards. I lead the Information Security Operations team, which protects the information assets and services of DPH, Zuckerberg San Francisco General Hospital, 55 behavioral health clinics, and joint research programs with the University of California, San Francisco. I provide leadership and guidance in critical areas of cybersecurity and technology administration, such as budgeting, resource development and allocation, governance and policy formation, technology evaluation, service development, delivery, and operations. I align cybersecurity priorities with agency operations goals and objectives and improve cost-effectiveness, service quality, and operational effectiveness. I have played a key role in critical projects, such as department reorganizations, infrastructure assessments, and technology refreshes. I have a proven background in helping organizations boost operational performance, enhance efficiency, drive down costs, and increase customer satisfaction by developing and executing IT strategy that produces business value.
My mission is to transform IT from an order-taking cost center to a strategic business partner and to deploy IT to create a competitive advantage in the healthcare market.”
About the City of San Francisco: San Francisco is a vibrant and dynamic city at the forefront of economic growth & innovation, urban development, arts & entertainment, social issues & change. This rich tapestry of culture and ideas is sustained by our City’s commitment to heightening the quality of life for San Franciscans and residents of the greater Bay Area. Our employees play an important role not only in making our City what it is today but also in shaping the future of San Francisco. The City & County of San Francisco employs more than 34,000 individuals in various services such as maintaining city streets and parks, driving buses and cable cars, providing public health services, keeping the streets safe, and firefighting.
Session Four – 11:15 AM to 12:15 PM | Keynote: Standards & the Future of AI, Cybersecurity | Sherri Douville and Steve Wilson
Cybersecurity and AI industry giants Steve Wilson and Sherri Douville present Standards & the Future of AI, Cybersecurity – the Full Tech Stack. As the founder of OWASP LLM Top 10, Steve’s work focuses on the many specifications we rely upon as cyber professionals.
Sherri Douville is the co-chair of IEEE/UL JV for the technical trust standard SG project for Clinical IoT in medicine, P2933. She is passionate about redefining technology, software, and data for medicine and advanced health technologies in a way worthy of the trust of clinicians, our families, and friends.
Steve Wilson will speak to the more practical actions available for developers and buyers of LLM applications today. Steven’s portion of the talk will include the most necessary steps identified by his industry-leading OWASP LLM team. (Read more LLM AI Security & Governance Checklist)
Cybersecurity and AI industry giants Steve Wilson and Sherri Douville present our keynote address, Standards & the Future of AI, Cybersecurity – Across the Full Tech Stack, as the founder of OWASP LLM Top 10. Sherri and Steve cover the impacts of today’s leading AI and Cybersecurity standards and what is predicted to be the dominant IEEE standard of our time.

About Sherri Douville:
Sherri Douville is the CEO of Medigram, the Mobile Medicine company dedicated to enhancing health systems’ safety, efficiency, and profitability. Additionally, she is the editor for the forthcoming 4th book on AI and Cybersecurity for Healthcare Boards. Sherri is a repeat editor and author of two long-term best-selling books, Mobile Medicine and Advanced Health Technology. She also holds the role of series editor with the top healthcare IT academic publisher, Taylor & Francis, based in the U.K.
Known for her ability to align engineering, IT, physician leaders, informatics, and legal professionals across the industry, Sherri co-chaired the first-of-its-kind multidisciplinary technical continuing medical education symposium with the Intelligent Health Association. The book series she oversees features a team of top experts in all relevant domains, comprising 100 coauthors and editorial reviewers, recognized as the premier ecosystem in the field. In her efforts to drive alignment beyond publications, Sherri is co-chair of trust for the industry’s IEEE technical standard. She also served on the healthcare CIO leadership group and CHIME certification committee for cybersecurity. Sherri has been honored to co-chair top industry conference tracks, with numerous speaking engagements, including keynotes, University lectures, and podcasts for various professional associations, governments, Ivy League institutions, and prestigious universities globally. Additionally, she has contributed to corporate board education for privacy and cybersecurity at Santa Clara University. https://www.medigram.com
About Medigram:
“We’re an experienced and passionate team driven by our vision to solve a leading cause of preventable death on par with most common cancers, including breast cancer, a delay in medical communication. Medigram provides a mobile communication app and platform for physicians, the only solution designed to work securely when no other healthcare apps can and with the security that medicine deserves built in at all solution levels. The Medigram system is designed to drive safety, efficiency, and profitability by leveraging cutting-edge technology, design thinking informed services, LEAN & 6 Sigma clinical operations program design, and multidisciplinary change management. Our implementation services and data with AI insights are built to drive better patient outcomes and financial results for our customer partners. We serve health systems that share our vision for the benefits that faster care brings towards improving quality and financial outcomes built on a foundation of market-leading security. This is unlike existing physician communication tools, which are not proven reliable and secure and do not possess the ability to deliver results for patients, physicians, and clients.
Why Medigram: Doctors need to get a hold of one another quickly. They can’t do so now because it routinely takes two or more hours for them to receive imessages or text messages that do not have medical-grade compliance and security. Medigram is engineered to work when nothing else does for the physician on mobile devices. Medigram is building compliance and security into all levels of the solution so that our customers can sleep at night as physicians increasingly demand mobility.
Our team has been in your shoes as Head of IT, Chief Medical Officer, and Head of Clinical Operations with clinical transformation programs and 200 LEAN 6 Sigma projects completed with over 40 health systems. We understand how to help you deliver results for your patients, physicians, and other stakeholders by leveraging technical excellence, governance, and implementation with world-class change management. The Medigram solution was 100% designed for physicians and your unique work environment and workflow. Everything from the Medigram technology to services is built to enable physicians to deliver faster, safer, and better patient care. The Medigram team brings decades of experience and networks in all corners of healthcare administration, IT, and medicine. We are veterans in enterprise mobile technologies and systems built for reliability and resilience. We are health system C-level IT executives, experienced operators, sales executives, technologists, physician executives, data experts, AI ethics, and policy geeks.

CPO at Exabeam | Lead for OWASP Top 10 for Large Language Model AI Security | Driving AI-Powered Product Innovation
About Steve Wilson: Chief Product Officer at Exabeam, Steve Wilson leads product strategy, product management, product marketing, and research. He is a leader and innovator in AI, cybersecurity, and cloud computing, with over 20 years of experience leading high-performance teams to build mission-critical enterprise software and high-leverage platforms. Before joining Exabeam, he served as CPO at Contrast Security, leading all aspects of product development, including strategy, product management, product marketing, product design, and engineering. Wilson has a proven track record of driving product transformation from on-premises legacy software to subscription-based SaaS business models, including at Citrix, accounting for over $1 billion in ARR. He has experience building software platforms at multi-billion dollar companies like Oracle and Sun Microsystems.
Wilson is also a project leader at the Open Web Application Security Project (OWASP) Foundation, where he has assembled a group of over 400 experts to create the first industry-standard, comprehensive reference project called the “Top 10 List for Large Language Model Applications.” The list educates developers, designers, architects, managers, and organizations about the potential security risks when deploying and managing generative AI and other large language models (LLMs). He holds a degree in Business Administration from the University of San Diego and a second-degree black belt from the American Taekwondo Association.
About OWASP: owasp.org The Open Worldwide Application Security Project is an online community that produces freely available articles, methodologies, documentation, tools, and technologies in the fields of IoT, system software, and web application security. The OWASP provides free and open resources.
About Exabeam: Exabeam is a global cybersecurity leader and creator of New-Scale SIEM™️. We help organizations detect threats, defend against cyberattacks, and defeat adversaries, offering a new way for security teams to approach threat detection, investigation, and response (TDIR). By combining the scale and power of the cloud with the strength of our industry-leading behavioral analytics and automation, organizations gain a more holistic view of security incidents, uncover anomalies missed by other tools, and achieve faster, more accurate, and repeatable responses.
Lunch on the Mezzanine at ZEISS

Lunch n’ Learn – Session Five + Second ZEISS Tour or Virtual Session
Our guests are served Chicken Souvlaki, Falafel, Grilled pita, classic hummus, kalamata olives, diced tomatoes, diced cucumbers, red onion, feta cheese, tzatziki, Greek salad, tabbouleh and individual water, a catered lunch in the beautiful ZEISS mezzanine.
Furthering our commitment to varied learning styles and supporting our goal for inclusion, global thought leader Sarah Clarke has pre-recorded exceptional conversations specifically targeting themes relevant to our day. Attendees can take a quiet break to Listen and Learn from Sarah Clarke, or they can stretch their legs by taking the second tour of ZEISS.
All ISC2 East Bay Chapter members are welcome to enjoy the recorded session.
Virtual Session: Make Space for Governance, Sarah Clarke, Technology Governance Specialist, CEO, InfoSpectives | (+1 CPE)
Sarah Clarke Data protection, security, AI/ML governance, risk, and compliance – Infospectives
Sarah Clarke brings meaningful insights, war stories, and actionable ideas from the modern tech jungle, all with a sense of humor. It comes from more than two decades of working to secure data in a world that changes at the speed of the internet.
Sarah is a technology ethicist and highly respected governance specialist. For the past 20 years, she has gained a rare breadth of insight into tackling risk and compliance in-depth, at speed, and at both startup and corporate scales. She is an award-winning blog writer, a frequent contributor to other publications, an international speaker, and a guest lecturer.
Sarah is a vocal advocate for respect for both human rights and ethics in technology while working to operationalize consideration of both. Her overarching aim is to make it simpler to do things in a secure and privacy-respecting way. Whether that be through smart simplification, clearer risk communication, maturing governance functions, or automation.
DISCLAIMER: Statement in error about a court case regarding Automattic
- During the talk, I referred to a court case regarding Automattic. the parent company that owns WordPress and Tumblr. This was incorrect. They were the subject of a recent news story alleging a deal with Microsoft to use content to train ChatGPT and Midjourney. This is their response: https://automattic.com/2024/02/27/protecting-user-choice/
- This article gives an overview: https://wptavern.com/automattic-faces-scrutiny-over-ai-access-policy.
- Restating, there is not a related lawsuit. I had seen the court case below alleging copyright infringement from the same trusted source and mistakenly confused the two. It was part of broader discussions about using copyright data, personal data, and intellectual property for model training.
- Intercept Media vs OpenAI (Intercept, Raw Story, AlterNet), California – https://www.loevy.com/wp-content/uploads/2024/02/Intercept-v.-OpenAI-Complaint-Filed.pdf
- Similar to the December 2023 New York Times Company vs. Microsoft and OpenAI case in federal district court – https://nytco-assets.nytimes.com/2023/12/NYT_Complaint_Dec2023.pdf
Session Six – 1:15 – 2:00 PM | Cyberthreats in modern healthcare – Kaiser Permanente, George D. DeCesare, JD, CISM | Senior Vice President
Chief Technology Risk Officer

George D. DeCesare joined Kaiser Permanente in 2015 as the organization’s Senior Vice President and Chief Technology Risk Officer, accountable for technology risk management for Kaiser Permanente. Emphasizing the privacy, security, and integrity of Kaiser Permanente and its member’s data while ensuring technology regulatory compliance, George leads cross-functional teams to promote mature risk management practices across the enterprise through the application of technology and the adoption of innovation. In this role, services are provided across Kaiser Permanente, covering its 12 million members, patients, clinicians, and customers, as well as services for its workforce and vendors. George has a wealth of experience leading this type of work across complex, large-scale organizations.
Prior to Kaiser Permanente, George had an expansive career as an executive working to design and implement various strategic-level programs, leveraging comprehensive frameworks to deliver the objectives, policies, procedures, and standards to address community, business, and organizational needs. Spanning over 20 years in the healthcare industry alone, he held various positions, including Chief Information Security Officer (CISO) and as an in-house counsel with a primary practice covering healthcare regulatory compliance, privacy, and cybersecurity law. George also served as a captain for the Los Angeles County Sheriff’s Department for 17 years. During his tenure there, he worked as an investigator specializing in identity theft crimes and served on the Advisory Council on Computer Forensics.
George holds a juris doctorate from Northwestern CU School of Law and a master’s in business from Columbia Pacific University. He has served on numerous boards in the healthcare and educational sectors. He is a member of the Healthcare Industry Cybersecurity Task Force formed by the U.S. Department of Health and Human Services. George also holds a long list of professional certifications and awards.
Kaiser Permanente – “We are relentless in our pursuit of excellence. Founded nearly 80 years ago, our unique business model sets us apart — positioning us to drive improvements across the industry and worldwide. As the nation’s leading not-for-profit health plan, we proudly serve 12.7 million members from 600+ locations in 8 states and Washington, D.C. Together, our 200,000+ employees and physicians work as one to positively impact the lives of our members, employees, and communities. Come drive quality, inspire excellence, and create change for the better. Bring your talents to Kaiser Permanente and see your visionary ideas make a difference in the lives of others. This is your opportunity to shape the future of health care.”
Session Seven – 2:00 to 2:30 PM | Healthcare is Hybrid | Cloud Security with Stephen Carn, Director Cloud Ops, Varian Medical Systems

Director, Cloud Operations at Varian Medical Systems
Stephen Carn is a well-respected professional with years of service among ISC2, ISACA, and ITSMF, certified in ITIL, an IT Service Visionary & Evangelist, and a Governance Evangelist – Cobit.
According to the AT&T Cybersecurity Insights Report: A Focus on Healthcare (att.com, 63.8% of healthcare organizations ranked attacks against server data at the network edge as cyber threats of their highest concern. 63.4% of healthcare organizations said attacks against associated cloud workloads were some of the riskiest future attacks against them. We’ve invited Stephen Carn to address the fact that Healthcare is hybrid and to suggest technology-driven governance that we should all have or soon have implemented.
About Varian—Now Part of Siemens Healthineers
Varian has long been on a mission to help create a world without fear of cancer. Now, as a Siemens Healthineers company, we are working as one, based on a more expansive perspective of the patient’s journey than ever before. As a result, our vision for the future – and what we can achieve on behalf of patients – has expanded and become much more comprehensive.
Given the broad portfolio of imaging and cancer care technologies and services we offer as one unified company, we are working to create an oncology ecosystem that enables us to support care providers along the entire cancer care continuum.
Our History
We’re proud of our pioneering history, helping to advance radiotherapy, radiosurgery, and many other vital cancer-fighting tools. We believe cancer is beatable, and we’re excited to see each new development that proves us right.
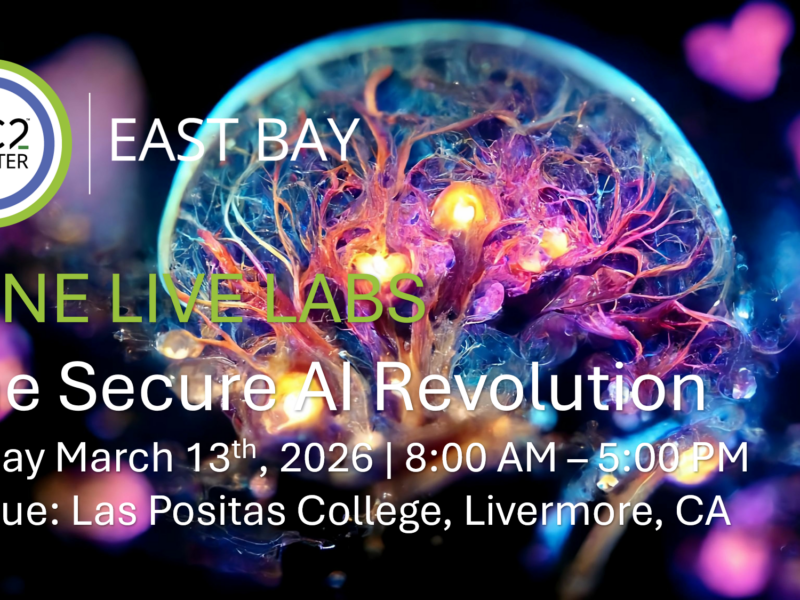
2:30 – 3:00 PM CAKE BREAK and Book Signing

Our Cake Breaks are legendary. It’s a good thing that ZEISS has plenty of stairs.
Advanced Health Technology: Managing Risk While Tackling Barriers to Rapid Acceleration – Get your signed copy | Purchase your copy now | Bring your book to the book signing at 2:30 and have your chance to speak with the Editor, Sherri Douville.
Although it’s too soon to purchase Steve Wilson’s entire volume, The Developer’s Playbook for Large Language Model Security, we encourage our attendees to sign-up for the O’REILLY Books trial subscription and enjoy the first several chapters for free.
Large language models (LLMs) are not just shaping the trajectory of AI, and they’re also unveiling a new era of security challenges. This practical book takes you straight to the heart of these threats. Author Steve Wilson, chief product officer at Exabeam, focuses exclusively on LLMs, eschewing generalized AI security to delve into the unique characteristics and vulnerabilities inherent in these models.
Complete with collective wisdom gained from creating the OWASP Top 10 for LLMs list—a feat accomplished by more than 400 industry experts—this guide delivers real-world guidance and practical strategies to help developers and security teams grapple with the realities of LLM applications. Whether you’re architecting a new application or adding AI features to an existing one, this book is your go-to resource for mastering the security landscape of the next frontier in AI.
Session Eight – 3:00 to 3:30 PM | The reason we are here: Mentoring and Internship – Meeting the Career Placement experts from Las Positas College and the ISC2 East Bay Members | How we create the Sponsors who successfully employ them.
As an alternative to the afternoon’s seated presentation sessions, a small interactive group between persons seeking internships, employment, or potential employers will be held in room two. Our Director of Career Development and various corporate volunteers look forward to speaking with the top five internship candidates. These lucky students will work with a team of ISC2 East Bay Directors throughout their academic year and earn placement for their summer semester. Additional meetings will be scheduled with all interested students as virtual sessions.

Beth McCormick, President of McCormick Consulting, provides strategic solutions that address chronic workforce challenges through community college partnerships. Previously, McCormick served as the director of Strategic Workforce Development for Engineering at the Lawrence Livermore National Laboratory. McCormick has over 20 years of developing workforce strategies in STEM fields.
Beth is known nationwide for spearheading the innovative Vets2Tech program, a two-year community college program that provides a pathway for veterans to gain living wage jobs in tech. The Obama administration recognized this program as a best practice. The East Bay Economic Development Association awarded it the 2017 Education Innovation Award.
Beth is passionate about providing career-enhancing opportunities in STEM to veterans, under-represented populations, and women. She believes employers need to be active partners with universities and community colleges when it comes to building America’s diversity pipeline. Applied learning through internships is the key to building a successful pipeline of students in STEM.
Beth recently served on advisory boards for California Polytechnic State University, UC San Diego, Ohlone College, and Las Positas College Foundation and is the past Chair of the Alameda County Workforce Development Board. Beth was named Mentor of the Year for the East Bay Society of Engineers in 2023. Beth currently serves as a board member of Innovation Tri-Valley and is President-elect of the Livermore Valley Rotary Club.
Beth has a degree in Chemical Engineering from Michigan State University.
Beth is accompanied by two members of the Las Positas staff, Moh Daoud and Carlos Morena.

Session Nine – 3:30 to 4:30 PM | Round Table – The current and future state of Healthcare & Healthtech – an open invitation to past presenters from our California Healthcare Providers – Calls to Action
Nalin Narayanam, Chief Information Officer, AdaptHealth – Moderator

Chief Information Officer, AdaptHealth



More about your panel:
Nalin Narayanam, Chief Information Officer at AdaptHealth, has over two decades of technology experience in multiple areas like Identity Management, Tokenization, DLP, and SIEM.
With a career spanning over three decades, I embarked on a journey in programming, evolving into a thought leader dedicated to leveraging the best technologies for the betterment of patients’ lives. Currently serving as the Chief Information Officer (CIO) for AdaptHealth, a prominent healthcare company specializing in sleep therapy, respiratory therapy, and diabetic supplies, my role is pivotal in advancing healthcare through technological excellence.
My trajectory at AdaptHealth began as the Chief Information Security Officer (CISO), where I fortified digital defenses before ascending to the role of CIO. This transition showcases my strategic leadership and adaptability in navigating the complex intersection of information security and healthcare technology.
In my extensive career, I’ve made significant contributions to Fortune companies such as CVS Caremark, BlueCross Blue Shield of MA, Discovery Channel, and Capital One. These experiences have enriched my expertise, allowing me to bring a wealth of knowledge to my current position. As CIO at AdaptHealth, I am dedicated to driving innovation and efficiency, ensuring that the company remains at the forefront of healthcare technology, ultimately making a positive impact on patient care.
Sherry Ryan is a Partner in Fortium Partners’ security practice, where she primarily serves technology, health care, and consumer products companies. She has built and managed world-class information security programs and technology teams for industry-leading companies, including Levi Strauss, Safeway, Hewlett-Packard, Blue Shield of California, and Juniper Networks. Her leadership in the field has been marked by notable awards, including Silicon Valley Women of Influence, National Diversity Council’s Top 50 Most Powerful Women in Tech, Top 50 Women in Internet Security, Technology Magazine’s Top 100 Women in Technology, 50 Influential CISOs and Cybersecurity Leaders to Follow, and Cyber Magazine’s Top Female Leaders in Cybersecurity. Sherry graduated with a Bachelor of Science in Business Administration from the University of Redlands and earned a Master of Business Administration from Notre Dame De Namur University. She serves on the advisory boards of SafeBreach, and YL Ventures and is an independent director of Secberus.
Amit Wasson has more than 25 years of IT experience, specializing in leading teams in the implementation of Cybersecurity programs that drive security awareness, reduce exposure, and strengthen the organization’s security posture. Working with organizations like Intuitive Surgical, KLA Tencor, Wells Fargo, and Hughes Communications, he has a successful track record of facilitating technology-business alignment while balancing risk exposure and corporate growth. Amit has obtained several cybersecurity certifications, including C|CISO, CISSP, CISM, CISA, and GIAC certifications.
Eddie Borrero is the chief information security officer for Blue Shield of California, which is an independent member of the Blue Shield Association and is a nonprofit health plan dedicated to providing Californians with access to high-quality health care at an affordable price.
As a thought leader in the industry with over 20 years of information security management experience, Eddie is completely inspired by the challenge of creating and growing information security practices and programs within large organizations – which fits nicely with his passion for managing and developing people. Eddie joined Blue Shield of California in 2020 and is responsible for the management of information security and compliance for the company. Before his current role, Eddie worked in governance, oversight, and management of enterprise information protection programs for Robert Half, Amgen, Electronic Arts, Intuit, and PG&E.
He is a Navy veteran who has broad experience working at a global level with start-ups as well as Fortune 500 companies. Eddie is a transformative global business leader and champion of diversity, equity, and inclusion who has over 25 years of experience managing technology, security, privacy, and risk teams
I love to make waves that shape the future for the better.
I am passionate about making a positive impact in the world through technology, leadership, and social justice. I have been a tech executive for over 20 years, working on products and services that improve the lives of millions of customers in various domains, such as finance, gaming, staffing, energy, and healthcare. I have also been involved in cyber security, product design, and non-profit board work, where I use research, relationships, and best practices to create and scale change globally. My motivation is to empower and guide the next generation of leaders, create new and innovative solutions, and promote diversity, equity, and inclusion.
Eddie Borrero
Recent past speakers are attending as our guests.
Thank you, gifts & Conference Feedback
To receive all 8 CPEs, attendees must complete the Conference Feedback Form. ISC2 East Bay Chapter is a nonprofit offering our community a safe networking experience where they can advance their interests and careers in cybersecurity. If you attend all sessions, attend the virtual session, and respond to the pre-conference educational challenge, you can earn up to 11 CPEs.
We regret that this venue is not large enough to accommodate our entire membership. However, we will post recorded sessions and a means for earning CPE.

ISC2 East Bay 2024 Sponsors
Platinum – Lifetime and Venue
- Stellar Cyber
- ZEISS (Venue)
- Securonix
- Oracle (Venue)
- CyberArk
- NetSkope
- SECLORE
Gold Sponsors (2K)
2024 Silver Sponsors (1K)
- Exiger
2024 Bronze Sponsors (500)
- Concentric.AI
- TalPoint
- StrongDM
- Advantage Technology
- Zyston LLC
- EnterpriseGRC Solutions
- Pantheon
Paying it forward
- Thank you to Symmetry Systems for your sponsorship to cover an attendee at this event.
Please become an ISC2 East Bay Sponsor by donating on our Sponsorship Page